Tuesday☕️

Trending:
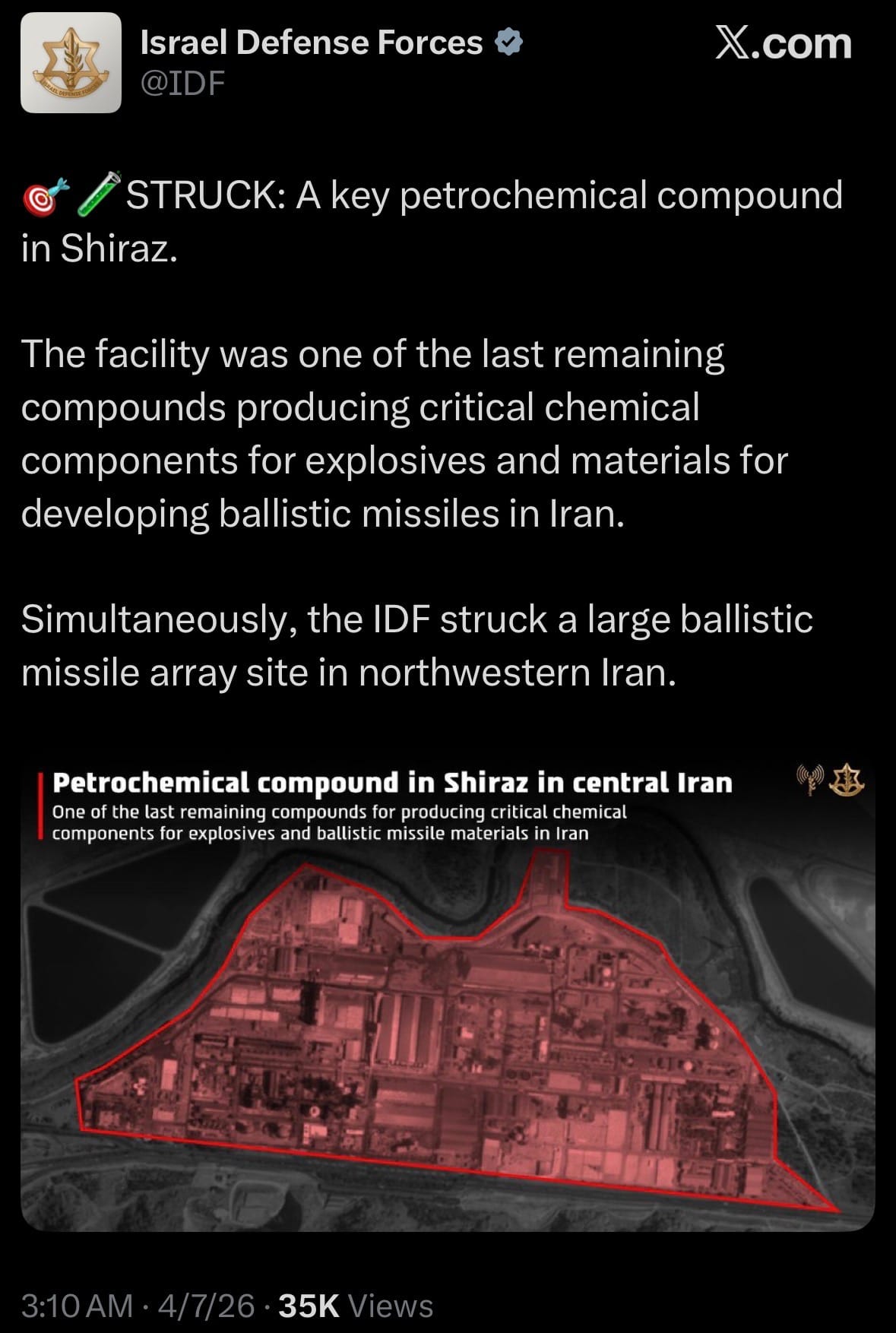
- In the past 24 hours, U.S. and Israeli forces struck Tehran’s Imam Khomeini International Airport and nearby military airfields, while Iran launched new missile and drone attacks on Israeli cities and Gulf energy/desalination plants. President Trump issued a strong ultimatum demanding Iran immediately reopen the Strait of Hormuz or face strikes on its power grid and oil terminals. Iran has rejected the demand so far.

- The Strait of Hormuz remains fully closed for the 34th straight day. Multiple nations, including the U.S., Germany, Japan, South Korea, India, and Saudi Arabia, have announced major increases in military spending and arms production in the last 24 hours. Europe and Asia are currently being hit the hardest economically by fuel shortages, surging energy prices, and rising food costs.
Economics & Markets



Geopolitics & Military Activity:

Environment & Weather:
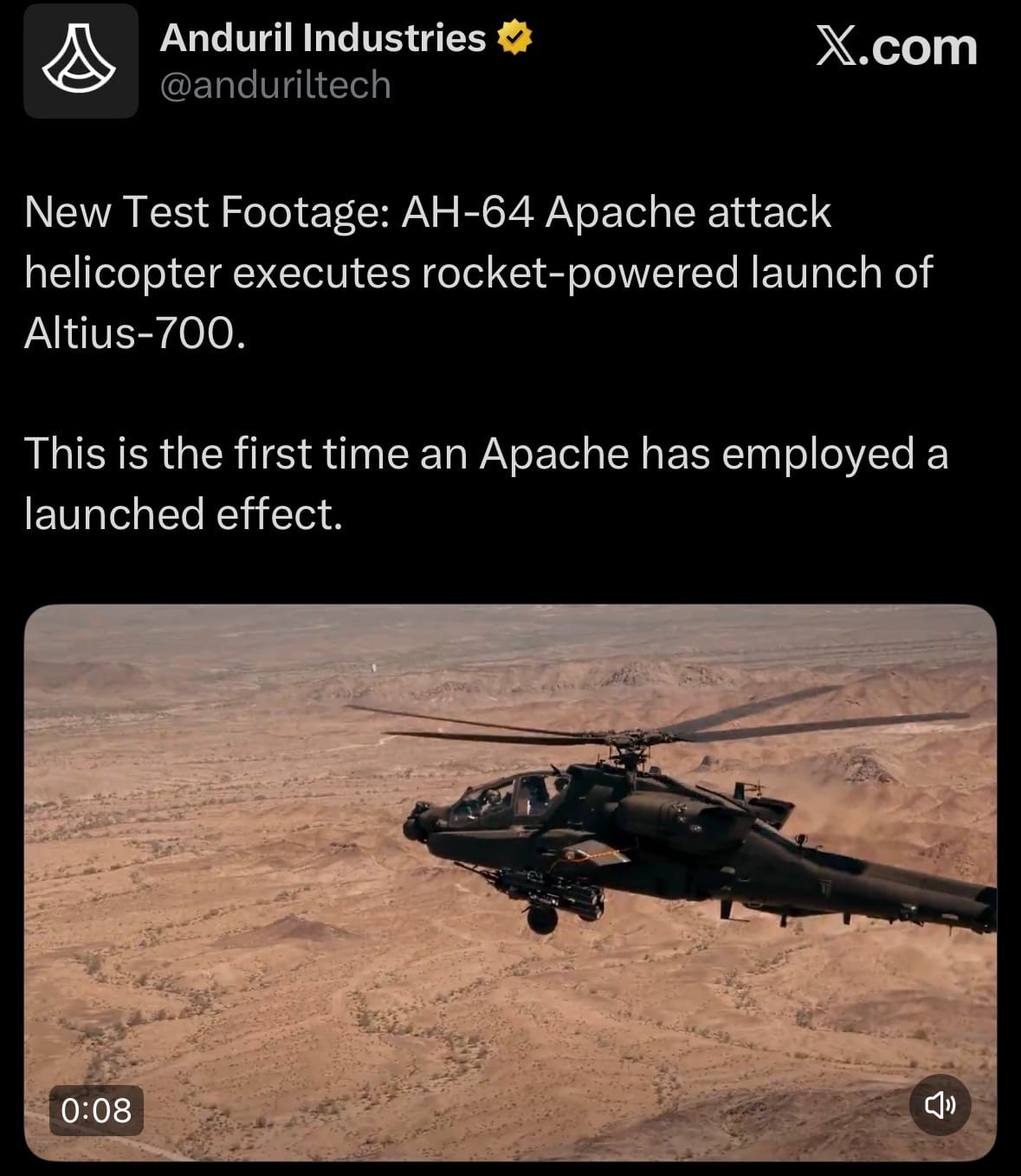
Science & Technology:

Space:
- As of April 7, 2026, NASA’s Artemis II mission is in its seventh day and proceeding smoothly.
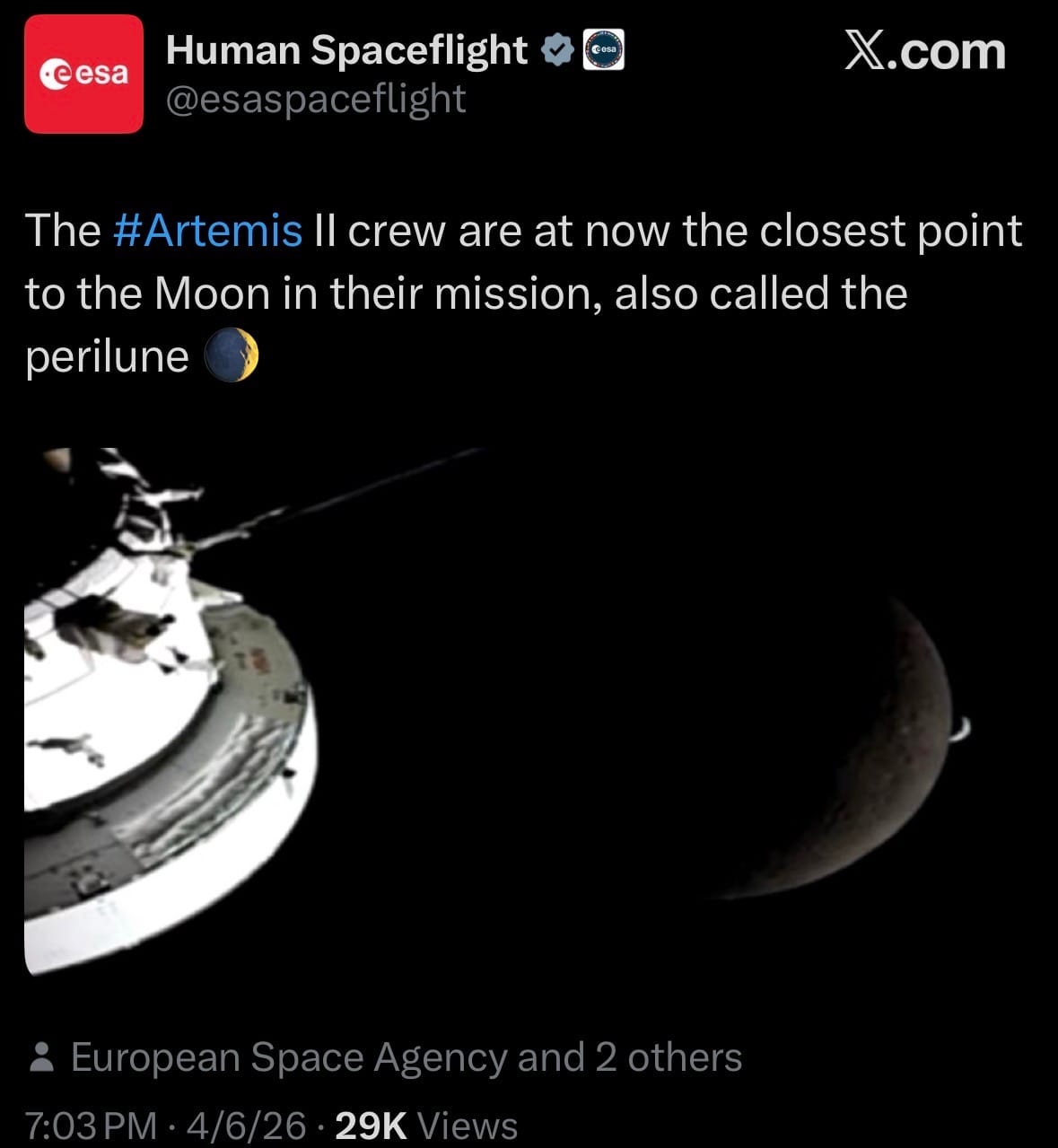
- The crew successfully completed their close lunar flyby yesterday, flying just 4,000 miles above the Moon’s surface and becoming the first humans in over 50 years to see the far side of the Moon with their own eyes. Orion is now on its return trajectory to Earth and remains on track for a splashdown off the coast of San Diego on April 10 or 11.
Statistic:
- Largest assets on Earth by market capitalization:
- Gold: $32.750T
- 🇺🇸 NVIDIA: $4.317T
- Silver: $4.108T
- 🇺🇸 Apple: $3.804T
- 🇺🇸 Alphabet (Google): $3.600T
- 🇺🇸 Microsoft: $2.771T
- 🇺🇸 Amazon: $2.284T
- 🇸🇦 Saudi Aramco: $1.784T
- 🇹🇼 TSMC: $1.772T
- 🇺🇸 Broadcom: $1.490T
- 🇺🇸 Meta Platforms: $1.449T
- Bitcoin: $1.379T
- 🇺🇸 Tesla: $1.323T
- 🇺🇸 Berkshire Hathaway: $1.027T
- 🇺🇸 Walmart: $1.010T
- 🇰🇷 Samsung: $874.12B
- 🇺🇸 Eli Lilly: $829.73B
- 🇺🇸 Vanguard S&P 500 ETF (VOO): $828.12B
- 🇺🇸 JPMorgan Chase: $796.83B
- 🇺🇸 iShares Core S&P 500 ETF (IVV): $729.63B
- 🇺🇸 Exxon Mobil: $680.72B
- 🇺🇸 SPDR S&P 500 ETF (SPY): $657.03B
- 🇺🇸 Visa: $584.83B
- 🇺🇸 Johnson & Johnson: $580.71B
- 🇺🇸 Vanguard Total Stock Market ETF (VTI): $568.21B
History:
- Cybersecurity began in the early days of computing when systems were isolated and threats were mostly theoretical rather than intentional. In the 1960s and early 1970s, large mainframe computers used by governments and universities started introducing basic access controls like passwords, but security wasn’t a major focus yet. That changed in 1971 with the creation of the Creeper virus, the first known self-replicating program, which spread across ARPANET (the precursor to the internet). Shortly after, the first antivirus program called Reaper was created to remove it, marking the beginning of offensive and defensive cyber dynamics. By the late 1970s and 1980s, as computers became more connected, security concerns grew—especially after the Morris Worm in 1988, which infected about 10% of the internet and led to the creation of the first Computer Emergency Response Team (CERT). During this period, foundational concepts like encryption standards (DES in 1977) and public-key cryptography (Diffie-Hellman in 1976, RSA in 1977) were developed, forming the backbone of modern digital security.
- In the 1990s and 2000s, cybersecurity evolved rapidly alongside the growth of the internet, shifting from isolated incidents to widespread global threats. Firewalls, intrusion detection systems, and antivirus software became standard as businesses moved online, but so did more sophisticated attacks like phishing, denial-of-service (DoS), and large-scale worms like ILOVEYOU (2000) and SQL Slammer (2003). The 2010s marked a major turning point, with cyber threats becoming highly organized, state-sponsored, and financially driven—examples include Stuxnet (2010), the first known cyberweapon targeting physical infrastructure, and massive data breaches like Target (2013) and Equifax (2017). Today, cybersecurity is a constant, evolving battlefield built around protecting data, systems, and infrastructure through layers of defense including encryption, identity management, behavioral monitoring, and AI-driven threat detection. Modern systems operate on the assumption that breaches will happen (“zero trust” architecture), focusing not just on prevention but on detection, response, and resilience, as cyber operations now span everything from individual identity theft to global cyber warfare.
Image of the day:

Thanks for reading! Earth is complicated, we make it simple.
- Click below if you’d like to view our free EARTH WATCH globe:

- Download our mobile app:


Click below to view our previous newsletters:
Support/Suggestions Email:
support@earthintel.io




